Pass4itsure shares a valid dump to help pass the CheckPoint 156-315.80 exam! The latest CheckPoint 156-315.80 VCE dumps and CheckPoint 156-315.80 PDF dumps, Pass4itsure CheckPoint 156-315.80 exam questions have been updated https://www.pass4itsure.com/156-315-80.html (439 Q&As Dumps)
Share free CheckPoint 156-315.80 exam tips questions and dumps – Pass4itsure
Free CheckPoint 156-315.80 exam pdf dumps download from Google Drive
[q1-q13, free pdf] CheckPoint 156-315.80 exam pdf dumps https://drive.google.com/file/d/1ZZi6iHYn8WHKPTm4X17It_tqANreINEj/view?usp=sharing
Practice CheckPoint 156-315.80 exam question 1-13
QUESTION 1
What is the mechanism behind Threat Extraction?
A. This a new mechanism which extracts malicious files from a document to use it as a counter-attack against its
sender.
B. This is a new mechanism which is able to collect malicious files out of any kind of file types to destroy it prior to
sending it to the intended recipient.
C. This is a new mechanism to identify the IP address of the sender of malicious codes and put it into the SAM
database (Suspicious Activity Monitoring).
D. Any active contents of a document, such as JavaScripts, macros and links will be removed from the document and
forwarded to the intended recipient, which makes this solution very fast.
Correct Answer: D
QUESTION 2
Which TCP port does the CPM process listen on?
A. 18191
B. 18190
C. 8983
D. 19009
Correct Answer: D
QUESTION 3
What has to be taken into consideration when configuring Management HA?
A. The Database revisions will not be synchronized between the management servers
B. SmartConsole must be closed prior to synchronized changes in the objects database
C. If you wanted to use Full Connectivity Upgrade, you must change the Implied Rules to allow FW1_cpredundant to
pass before the Firewall Control Connections.
D. For Management Server synchronization, only External Virtual Switches are supported. So, if you wanted to employ
Virtual Routers instead, you have to reconsider your design.
Correct Answer: A
QUESTION 4
Check Point ClusterXL Active/Active deployment is used when:
A. Only when there is Multicast solution set up.
B. There is Load Sharing solution set up.
C. Only when there is Unicast solution set up.
D. There is High Availability solution set up.
Correct Answer: B
QUESTION 5
Fill in the blank: A new license should be generated and installed in all of the following situations EXCEPT when
________ .
A. The license is attached to the wrong Security Gateway.
B. The existing license expires.
C. The license is upgraded.
D. The IP address of the Security Management or Security Gateway has changed.
Correct Answer: A
QUESTION 6
Which is NOT a SmartEvent component?
A. SmartEvent Server
B. Correlation Unit
C. Log Consolidator
D. Log Server
Correct Answer: C
QUESTION 7
When users connect to the Mobile Access portal they are unable to open File Shares.
Which log file would you want to examine?
A. cvpnd.elg
B. httpd.elg
C. vpnd.elg
D. fw.elg
Correct Answer: A
QUESTION 8
Which of these is an implicit MEP option?
A. Primary-backup
B. Source address based
C. Round robin
D. Load Sharing
Correct Answer: A
Reference: https://sc1.checkpoint.com/documents/R77/CP_R77_VPN_AdminGuide/13812.htm
QUESTION 9
What CLI utility runs connectivity tests from a Security Gateway to an AD domain controller?
A. test_connectivity_ad –d
B. test_ldap_connectivity –d
C. test_ad_connectivity –d
D. ad_connectivity_test –d
Correct Answer: C
Reference: https://sc1.checkpoint.com/documents/R80.30/WebAdminGuides/EN/CP_R80.30_CLI_ReferenceGuide/html_frameset.htm?topic=documents/R80.30/WebAdminGuides/EN/CP_R80.30_CLI_ReferenceGuide/200877
QUESTION 10
How many policy layers do Access Control policy support?
A. 2
B. 4
C. 1
D. 3
Correct Answer: A
Two policy layers:
-Network Policy Layer
-Application Control Policy Layer
QUESTION 11
You want to store the GAIA configuration in a file for later reference. What command should you use?
A. write mem
B. show config -f
C. save config -o
D. save configuration
Correct Answer: D
QUESTION 12
What does the Log “Views” tab show when SmartEvent is Correlating events?
A. A list of common reports
B. Reports for customization
C. Top events with charts and graphs
D. Details of a selected logs
Correct Answer: D
QUESTION 13
Which TCP-port does CPM process listen to?
A. 18191
B. 18190
C. 8983
D. 19009
Correct Answer: D
Reference: https://www.checkpoint.com/downloads/products/r80.10-security-management-architecture-overview.pdf
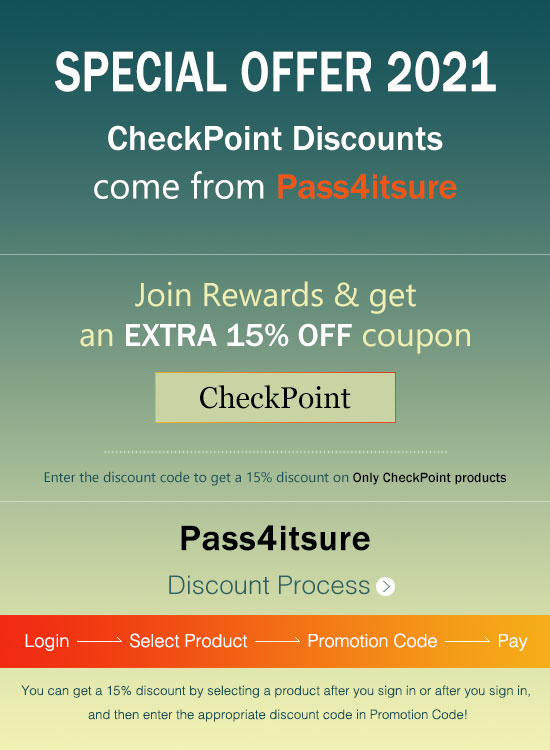
Pass4itsure CheckPoint dumps discount code 2021
The last sentence:
Latest update Pass4itsure CheckPoint 156-315.80 exam dumps: https://www.pass4itsure.com/156-315-80.html
Free CheckPoint 156-315.80 pdf dumps: https://drive.google.com/file/d/1ZZi6iHYn8WHKPTm4X17It_tqANreINEj/view?usp=sharing
The latest CheckPoint 156-315.80 exam questions can help you pass the exam! Trust Pass4itsure to help you pass the exam 100%!
